Risky about risk
27. marca 2025
(and similar concepts)
doc. Ing. Jaroslav Sivák, CSc., MBA
1. Introduction
This article deals with reflections on the basic concepts common in security practice. We consider "assets," "risk," "threat," "vulnerability," "resilience," and others as the basic concepts in security practice.
Why "risky" about risk and similar concepts? There are a large number of various academic works that deal with the definition of these concepts. Terminological dictionaries that have been approved by opposition councils are known, and the legal norms of the Slovak Republic also operate with these concepts. And yet, several binding sources differ. The European Union with its bodies has also contributed significantly to the definition of basic concepts in security management. Several directives use their own definitions of these concepts. These "European" concepts are often then implemented into our norms and into the vocabulary, especially of crisis managers.
"Risky" therefore because the claims contained in this article may not please my esteemed academic colleagues, workers especially from force departments who created and use (or don't use) terminological dictionaries and create laws and other legal norms in the field of security, and many others.
In an effort to express a certain reality as originally as possible, words such as "attack vector" enter the vocabulary of the security community. Certainly, if we try, we can find an analogy with the mathematical definition of "vector." But is it necessary...
It is not important whether a given concept is etymologically, grammatically, semantically, and otherwise, the most correct one. It is important that the community that works in security management understands each other and that under a given concept we can imagine as faithfully as possible what the author wanted to express by it and, ultimately, what it describes.
2. Basic Security Truth
The basic security truth, on which most stakeholders agree, is that RISK is the probability (or rate) that a THREAT will exploit a VULNERABILITY of an ASSET and cause an IMPACT on it.
This formulation expresses that we are trying to express a suitable interpretation of a measure that will most faithfully describe what can happen (and will happen) when the variables of this functional 1 reach certain values. Risk can be understood as a probability, or another value in the metric that we choose and that will correspond to objective reality and allow us to make judgments about the value - the extent of the impacts that threaten us.
The basic security truth includes both external and internal conditions for the occurrence of a security event. The external condition is THREAT. The internal condition is VULNERABILITY. The subject of the process is an ASSET that is exposed to a THREAT and is VULNERABLE. The result of a THREAT attack that exploited a VULNERABILITY and affects an ASSET is IMPACT. Upon closer examination of security event processes, we would come to other concepts, such as RESILIENCE.
Let's start from the concept of SECURITY. SECURITY is, quote: "A state of a social, natural, technical, technological system or other system that, in specific internal and external conditions, enables the fulfillment of specified functions and their development in the interest of man and society" 2 . Critical note: SECURITY cannot be a state! It is a dynamic process whose parameters are of a probabilistic nature. It is therefore a PROCESS. Security is a process that has certain boundaries of minimum and maximum realistically achievable security. This means that there is a non-zero tolerance for disruption of the nominal state. The system must be designed and constructed (arranged) so that it can function even when deviated from this equilibrium state within the range of the above min and max values. These factors can be referred to as RESILIENCE 3 .
In the following text, we will debate about the part of the basic security truth concerning the concept of RISK.
3. Risk
If we borrow the bon mot about what intelligence is, that it is what is measured by the intelligence quotient, then risk is what is determined by risk analysis.
Risk is, quote: "A measure of threat expressed by the probability of the occurrence of an undesirable phenomenon and its consequences" 4 . Another definition, quote: "By risk (we understand) the potential for loss or disruption due to a cyber security incident expressed as a combination of the extent of such loss or disruption and the probability of occurrence of a cyber security incident" 5 . In this sentence, only the "probability of occurrence..." is a measurable variable. The rest is immeasurable. How is it then possible to determine risk in the area of, for example, cyber security?
There are more daring definitions, which probably also give rise to the statement described above:
This article deals with reflections on the basic concepts common in security practice. We consider "assets," "risk," "threat," "vulnerability," "resilience," and others as the basic concepts in security practice.
Why "risky" about risk and similar concepts? There are a large number of various academic works that deal with the definition of these concepts. Terminological dictionaries that have been approved by opposition councils are known, and the legal norms of the Slovak Republic also operate with these concepts. And yet, several binding sources differ. The European Union with its bodies has also contributed significantly to the definition of basic concepts in security management. Several directives use their own definitions of these concepts. These "European" concepts are often then implemented into our norms and into the vocabulary, especially of crisis managers.
"Risky" therefore because the claims contained in this article may not please my esteemed academic colleagues, workers especially from force departments who created and use (or don't use) terminological dictionaries and create laws and other legal norms in the field of security, and many others.
In an effort to express a certain reality as originally as possible, words such as "attack vector" enter the vocabulary of the security community. Certainly, if we try, we can find an analogy with the mathematical definition of "vector." But is it necessary...
It is not important whether a given concept is etymologically, grammatically, semantically, and otherwise, the most correct one. It is important that the community that works in security management understands each other and that under a given concept we can imagine as faithfully as possible what the author wanted to express by it and, ultimately, what it describes.
2. Basic Security Truth
The basic security truth, on which most stakeholders agree, is that RISK is the probability (or rate) that a THREAT will exploit a VULNERABILITY of an ASSET and cause an IMPACT on it.
This formulation expresses that we are trying to express a suitable interpretation of a measure that will most faithfully describe what can happen (and will happen) when the variables of this functional 1 reach certain values. Risk can be understood as a probability, or another value in the metric that we choose and that will correspond to objective reality and allow us to make judgments about the value - the extent of the impacts that threaten us.
The basic security truth includes both external and internal conditions for the occurrence of a security event. The external condition is THREAT. The internal condition is VULNERABILITY. The subject of the process is an ASSET that is exposed to a THREAT and is VULNERABLE. The result of a THREAT attack that exploited a VULNERABILITY and affects an ASSET is IMPACT. Upon closer examination of security event processes, we would come to other concepts, such as RESILIENCE.
Let's start from the concept of SECURITY. SECURITY is, quote: "A state of a social, natural, technical, technological system or other system that, in specific internal and external conditions, enables the fulfillment of specified functions and their development in the interest of man and society" 2 . Critical note: SECURITY cannot be a state! It is a dynamic process whose parameters are of a probabilistic nature. It is therefore a PROCESS. Security is a process that has certain boundaries of minimum and maximum realistically achievable security. This means that there is a non-zero tolerance for disruption of the nominal state. The system must be designed and constructed (arranged) so that it can function even when deviated from this equilibrium state within the range of the above min and max values. These factors can be referred to as RESILIENCE 3 .
In the following text, we will debate about the part of the basic security truth concerning the concept of RISK.
3. Risk
If we borrow the bon mot about what intelligence is, that it is what is measured by the intelligence quotient, then risk is what is determined by risk analysis.
Risk is, quote: "A measure of threat expressed by the probability of the occurrence of an undesirable phenomenon and its consequences" 4 . Another definition, quote: "By risk (we understand) the potential for loss or disruption due to a cyber security incident expressed as a combination of the extent of such loss or disruption and the probability of occurrence of a cyber security incident" 5 . In this sentence, only the "probability of occurrence..." is a measurable variable. The rest is immeasurable. How is it then possible to determine risk in the area of, for example, cyber security?
There are more daring definitions, which probably also give rise to the statement described above:
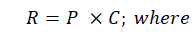
[1]
Let's imagine an example according to relation [1]:
The probability that an airplane will "fall" is 1 fall per 2 to 3 million flights (regardless of distance) 6 . The probability of an accident per flight is therefore (let's calculate the variant that 2 million flights):
- R is risk,
- P is the probability that a security incident will occur,
- C is the measure of impact (often only "negative" is meant).
Let's imagine an example according to relation [1]:
The probability that an airplane will "fall" is 1 fall per 2 to 3 million flights (regardless of distance) 6 . The probability of an accident per flight is therefore (let's calculate the variant that 2 million flights):
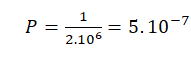
[2]
If the total damage quantified in money (C) was, for example, 50 million of currency (large aircraft, many victims, loss of Goodwill of the airline...), then according to [1] we should not sit in any airplane.
Correctly, in relation [1] another dimension of considerations is missing, and that is time . The probability that a security incident will occur must be measured in time, i.e., if the probability that there will be a breach of, for example, the perimeter of the digital world (cyber security of the network) is e.g., 0.5, we rightfully ask: "Over what period?" Definitely, relation [1] is not the best. A somewhat better approach would be Bayesian statistics, where risk is defined as the expected value of the loss function. Then there is the area of finance, where Value at Risk (VaR) is often used, which gives the maximum expected loss at a given level of reliability.
In probability theory, we often rely on the so-called probability distribution of the occurrence of a value. In security applications, it is better to use Poisson distributions rather than Gaussian ones, because security processes are burdened with "noise," i.e., a larger number of factors that also have a probabilistic character are at play.
Let's use the Poisson approach (we're looking for the probability of an event over time):
If we assume that an event occurs randomly with an average intensity λ (number of events per unit of time), then the probability that the event will occur exactly k times during a time interval t is given by the Poisson distribution:
Correctly, in relation [1] another dimension of considerations is missing, and that is time . The probability that a security incident will occur must be measured in time, i.e., if the probability that there will be a breach of, for example, the perimeter of the digital world (cyber security of the network) is e.g., 0.5, we rightfully ask: "Over what period?" Definitely, relation [1] is not the best. A somewhat better approach would be Bayesian statistics, where risk is defined as the expected value of the loss function. Then there is the area of finance, where Value at Risk (VaR) is often used, which gives the maximum expected loss at a given level of reliability.
In probability theory, we often rely on the so-called probability distribution of the occurrence of a value. In security applications, it is better to use Poisson distributions rather than Gaussian ones, because security processes are burdened with "noise," i.e., a larger number of factors that also have a probabilistic character are at play.
Let's use the Poisson approach (we're looking for the probability of an event over time):
If we assume that an event occurs randomly with an average intensity λ (number of events per unit of time), then the probability that the event will occur exactly k times during a time interval t is given by the Poisson distribution:
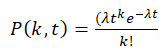
[3]
Using this mathematical model and our example, we would calculate that the probability that no accident will occur is approximately ≈0.99995 and the probability that at least one will occur (complement to one) ≈0.00005.
With such mathematical instruments, we would be able to predict quite accurately with what probability and over what time period a security incident will occur (and how many times it will repeat in a given time interval). The question remains with what probability in a certain time interval this event will occur. First occurrence?
If we are interested in the probability that an event will not occur until time t, we use the exponential distribution, which models the time until the first event:
- k is the number of occurrences of the event in time t,
- λ is the average number of events per unit of time,
- t is the length of the time interval.
Using this mathematical model and our example, we would calculate that the probability that no accident will occur is approximately ≈0.99995 and the probability that at least one will occur (complement to one) ≈0.00005.
With such mathematical instruments, we would be able to predict quite accurately with what probability and over what time period a security incident will occur (and how many times it will repeat in a given time interval). The question remains with what probability in a certain time interval this event will occur. First occurrence?
If we are interested in the probability that an event will not occur until time t, we use the exponential distribution, which models the time until the first event:
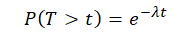
[4]
If someone wanted to complete our example, then they would calculate that the probability that the event will occur within two years is ≈0.632.
4. Risk in Practice
We have shown that there are relatively precise, but also complex mathematical approaches to determining (calculating) the value of the RISK parameter. However, for common security practice, this approach is awkward, especially for objects with a lower degree of importance. For high-risk objects (e.g., nuclear industry objects), specific (often classified) methodologies are used.
In practice, ready-made software tools for risk assessment, of which there are many, can be used. It is also possible to use your own risk analysis model, then it is necessary to consider especially:
Notes
Source: Sivák, Jaroslav. “RISKY ABOUT RISK.” Decent Cybersecurity, March 16, 2025. https://decentcybersecurity.eu/risk-interpretation-in-security/#324c01ae-6125-4551-9e96-2365485be6a2-link. Accessed: 27. 3. 2025
4. Risk in Practice
We have shown that there are relatively precise, but also complex mathematical approaches to determining (calculating) the value of the RISK parameter. However, for common security practice, this approach is awkward, especially for objects with a lower degree of importance. For high-risk objects (e.g., nuclear industry objects), specific (often classified) methodologies are used.
In practice, ready-made software tools for risk assessment, of which there are many, can be used. It is also possible to use your own risk analysis model, then it is necessary to consider especially:
- The significance of the organization/system, its attractiveness to the attacker. However, it is necessary to strictly consider the possibility that the organization/system will be used only as the first link in the attack, or as a maneuver to divert attention.
- Set the values of impacts that are acceptable for the organization (it can cover them with its resource capacity) and unacceptable. It is appropriate to develop a differentiated structure of impacts.
- Determine other parameters (assets, threats, vulnerabilities) according to the security analysis.
- Establish a scale for risk assessment (numerical or descriptive). Calculate or determine the risk values on this scale.
- The most important step is the interpretation of the risk value from which the level of acceptable risk will result.
- Establish risk management for risks that are unacceptable and need to be covered by defensive measures.
Notes
- A functional is a mathematical concept – it is a function that takes a function as input and returns a number.
- Terminological dictionary of crisis management. Security Council of the Slovak Republic. Bratislava 2017. p.8
- Ibid. p.24
- Ibid. p.26
- Act 366/2024 Coll. on cyber security. Collection of laws of the Slovak Republic §3, letter i)
- https://asn.flightsafety.org/
Source: Sivák, Jaroslav. “RISKY ABOUT RISK.” Decent Cybersecurity, March 16, 2025. https://decentcybersecurity.eu/risk-interpretation-in-security/#324c01ae-6125-4551-9e96-2365485be6a2-link. Accessed: 27. 3. 2025

The Critical Infrastructure Association of the Slovak Republic continues its series of articles introducing both the public and the professional community to the individual sectors of critical infrastructure as defined by Act No. 367/2025 Coll. on Critical Infrastructure and on Amendments to Certain Acts. Following sectors such as energy, transport and finance, we now turn to a sector that is part of the daily life of citizens as well as the functioning of the state – postal services.

Asociácia kritickej infraštruktúry Slovenskej republiky pokračuje v sérii článkov, ktorými verejnosti aj odbornej obci predstavuje jednotlivé sektory kritickej infraštruktúry definované zákonom č. 367/2025 Z. z. o kritickej infraštruktúre a o zmene a doplnení niektorých zákonov. Po sektoroch ako energetika, doprava či financie sa tentoraz venujeme sektoru, ktorý je súčasťou každodenného života občanov aj fungovania štátu – poštovým službám.

Until recently, the security of critical infrastructure was associated mainly with the protection of physical facilities, energy sources, or state systems. Today, however, it is increasingly clear that the real vulnerability often lies outside the organisation itself: in its supply chains, technology partners, and external services.

Ešte donedávna sa bezpečnosť kritickej infraštruktúry spájala najmä s ochranou fyzických objektov, energetických zdrojov či štátnych systémov. Dnes však čoraz jasnejšie vidíme, že skutočná zraniteľnosť sa často nachádza mimo samotnej organizácie: v jej dodávateľských reťazcoch, technologických partneroch a externých službách.
V januári 2024 zamestnanec finančnej spoločnosti v Hongkongu uskutočnil prevod v hodnote 25 miliónov amerických dolárov. Urobil tak po videokonferencii s finančným riaditeľom a kolegami z centrály, ktorá pôsobila úplne autenticky. Na konferencii však bol jediný skutočný človek on sám. Ostatní účastníci boli deepfake repliky vygenerované generatívnou umelou inteligenciou na základe verejne dostupných záznamov. Tento prípad, zdokumentovaný hongkonskou políciou, neoznámil príchod novej hrozby. Oznámil, že hrozba je už tu a funguje v produkčnom režime.

The Critical Infrastructure Association of the Slovak Republic is proud to present the success of two of its members, Decent Cybersecurity s. r. o. and FREQUENTIS Solutions & Services s. r. o., which have jointly secured funding for the four-year research and development project COSMOS-SECURE. The project, with total eligible expenditures of EUR 4,144,273.37 and a requested non-repayable financial contribution of EUR 2,981,048.65, focuses on an area that, until recently, belonged mainly to major space agencies: secure voice communication between ground stations, satellites, and spacecraft crews in an era when quantum computers are beginning to challenge the existing foundations of cryptography.

Asociácia kritickej infraštruktúry Slovenskej republiky s hrdosťou predstavuje úspech dvoch svojich členov, spoločností Decent Cybersecurity s. r. o. a FREQUENTIS Solutions & Services s. r. o., ktoré spoločne získali financovanie pre štvorročný výskumno-vývojový projekt COSMOS-SECURE. Projekt s celkovými oprávnenými výdavkami vo výške 4 144 273,37 € a požadovanou výškou nenávratného finančného príspevku 2 981 048,65 € sa zameriava na to, čo bolo donedávna doménou veľkých vesmírnych agentúr: bezpečnú hlasovú komunikáciu medzi pozemnými strediskami, satelitmi a posádkami vesmírnych lodí v ére, keď kvantové počítače začínajú spochybňovať existujúce kryptografické základy.

The Slovak Republic is in the final phase of a process that is fundamentally changing the approach to the protection of critical infrastructure. In accordance with Act No. 367/2024 Coll. on Critical Infrastructure, the list of entities that will be officially identified as critical for the functioning of the state is to be completed in July 2026. This step represents one of the most important milestones in the implementation of the new regulatory framework, the aim of which is to increase the resilience of key systems to crises, cyber threats and service outages. A new framework of responsibility Inclusion among the critical entities will not be of a merely formal nature. For the organisations concerned, it will mean the introduction of precisely defined obligations in the area of risk management, security measures, incident management and the very continuity of the provision of essential services within the meaning of the Act. For many entities, this represents a fundamental change in the approach to security, which will require systematic preparation even before the actual inclusion in the list. Growing interest of companies in the regulation Already in this period it is evident that potentially affected entities are beginning to intensively follow the development of the legislation and of the implementing rules being prepared. The reason is the need to set up internal processes in good time, so that the transition to the new regime can take place without major operational complications. The growing demanding nature of the requirements is at the same time increasing the demand for expert guidance and methodological support. The role of the Critical Infrastructure Association of the Slovak Republic In this context, the Critical Infrastructure Association of the Slovak Republic (AKI SR) plays a significant role, as it has long been creating a professional platform for cooperation between the state sector, regulators and operators of essential services across all sectors of critical infrastructure, such as for example energy, transport, healthcare or digital infrastructure. As Tibor Straka, President of AKI SR, states: “The process of identifying critical entities is not merely a legislative obligation. It is the moment that determines how resilient the state will be in real crisis situations.” The Association points out in this connection that the period before the final inclusion in the list is the most important one for organisations from the point of view of preparation and adaptation. Room for timely preparation Companies that may be part of the list of critical entities currently have a unique opportunity to prepare for the new obligations systematically and well in advance. In this area, AKI SR provides expert support, methodological guidance and a platform for the sharing of experience between the individual sectors. Cooperation as the foundation of resilience The implementation of the new system for the protection of critical infrastructure will be successful only if it is built on close cooperation between the public and the private sector. In this respect, AKI SR is developing a systematic dialogue with the central bodies of state administration that exercise state administration in the individual segments of critical infrastructure. With many of them, the Association has concluded memoranda of cooperation, which makes possible a more effective interconnection of expert capacities, the exchange of information and coordination in addressing key security topics. In the process, AKI SR thus acts as a natural communication and expert bridge between the regulator and the entities of critical infrastructure, while helping to connect legislative requirements with their practical implementation in the individual sectors. A new stage in the protection of critical systems The finalisation of the list of critical entities in July 2026 represents a fundamental step in the modernisation of the system for strengthening the resilience of critical infrastructure in Slovakia. The new legislative framework sets clearer rules, but at the same time significantly raises the demands placed on the preparedness of the organisations concerned. The outcome of the entire process will depend on how well it is possible to align the regulation with the reality of the operation of critical entities.

Slovenská republika sa nachádza v záverečnej fáze procesu, ktorý zásadne mení prístup k ochrane kritickej infraštruktúry. V súlade so zákonom č. 367/2024 Z. z. o kritickej infraštruktúre má byť v júli 2026 dokončený zoznam subjektov, ktoré budú oficiálne identifikované ako kritické pre fungovanie štátu. Tento krok predstavuje jeden z najdôležitejších míľnikov implementácie nového regulačného rámca, ktorý má za cieľ zvýšiť odolnosť kľúčových systémov voči krízam, kybernetickým hrozbám a výpadkom služieb. Nový rámec zodpovednosti Zaradenie medzi kritické subjekty nebude mať len formálny charakter. Pre dotknuté organizácie bude znamenať zavedenie presne definovaných povinností v oblasti riadenia rizík, bezpečnostných opatrení, incident manažmentu a samotnej kontinuity poskytovania základných služieb v zmysle zákona. Pre mnohé subjekty ide o zásadnú zmenu prístupu k bezpečnosti, ktorá si bude vyžadovať systematickú prípravu ešte pred samotným zaradením do zoznamu. Zvyšujúci sa záujem firiem o reguláciu Už v tomto období je zrejmé, že potenciálne dotknuté subjekty začínajú intenzívne sledovať vývoj legislatívy a pripravovaných vykonávacích pravidiel. Dôvodom je potreba včas nastaviť interné procesy tak, aby prechod do nového režimu prebehol bez zásadných prevádzkových komplikácií. Rastúca náročnosť požiadaviek zároveň zvyšuje dopyt po odbornom vedení a metodickej podpore. Úloha Asociácie kritickej infraštruktúry SR V tomto kontexte zohráva významnú rolu Asociácia kritickej infraštruktúry Slovenskej republiky (AKI SR) , ktorá dlhodobo vytvára odbornú platformu pre spoluprácu medzi štátnym sektorom, regulátormi a prevádzkovateľmi základných služieb naprieč všetkými sektormi kritickej infraštruktúry, ako je napríklad energetika, doprava, zdravotníctvo či digitálna infraštruktúra. Ako uvádza prezident AKI SR Tibor Straka: „Proces identifikácie kritických subjektov nie je len legislatívna povinnosť. Je to moment, ktorý určuje, ako odolný bude štát v reálnych krízových situáciách.“ Asociácia v tejto súvislosti upozorňuje, že obdobie pred finálnym zaradením do zoznamu je pre organizácie najdôležitejšie z hľadiska prípravy a adaptácie. Priestor na včasnú prípravu Firmy, ktoré môžu byť súčasťou zoznamu kritických subjektov, majú v súčasnosti jedinečnú príležitosť pripraviť sa na nové povinnosti systematicky a s dostatočným predstihom. AKI SR v tejto oblasti poskytuje odbornú podporu, metodické usmernenia a platformu na zdieľanie skúseností medzi jednotlivými sektormi. Spolupráca ako základ odolnosti Implementácia nového systému ochrany kritickej infraštruktúry bude úspešná len vtedy, ak bude postavená na úzkej spolupráci medzi verejným a súkromným sektorom. V tomto smere AKI SR rozvíja systematický dialóg s ústrednými orgánmi štátnej správy, ktoré vykonávajú štátnu správu na jednotlivých úsekoch kritickej infraštruktúry. S mnohými z nich má asociácia uzatvorené memorandá o spolupráci, čo umožňuje efektívnejšie prepájanie odborných kapacít, výmenu informácií a koordináciu pri riešení kľúčových bezpečnostných tém. AKI SR tak v procese vystupuje ako prirodzený komunikačný a odborný most medzi regulátorom a subjektami kritickej infraštruktúry, pričom pomáha prepájať legislatívne požiadavky s ich praktickou implementáciou v jednotlivých sektoroch. Nová etapa ochrany kritických systémov Finalizácia zoznamu kritických subjektov v júli 2026 predstavuje zásadný krok v modernizácii systému zvyšovania odolnosti kritickej infraštruktúry na Slovensku. Nový legislatívny rámec nastavuje jasnejšie pravidlá, ale zároveň výrazne zvyšuje nároky na pripravenosť dotknutých organizácií. Výsledok celého procesu bude závisieť od toho, ako dobre sa podarí zosúladiť reguláciu s realitou prevádzky kritických subjektov.

In August 2023, something happened on the Polish railways that until then had belonged to the realm of scenarios, not reality. Unknown actors abused the radio system for emergency stopping (radio-stop) and transmitted a signal that brought more than 20 trains to a halt in various regions of the country. The attack required no access to digital systems and no sophisticated malware. A radio transmitter and knowledge of publicly available tones were enough. It was a demonstration of why rail transport ranks among the most complex categories of critical infrastructure. It brings together older analogue and radio technology with contemporary IT and OT systems, and each of these layers has its own vulnerabilities.


