When hackers cut through the open path: inside the 95 million euro per day crisis at Jaguar Land Rover
The halt of global production at Jaguar Land Rover due to a cyberattack reveals an uncomfortable truth about modern industry. When hackers can paralyze assembly lines from Britain to Slovakia with just a few keyboard clicks, it testifies to a fundamental shift in industrial vulnerability.
Let's look at the mathematics of disruption. JLR achieves annual revenues of approximately 35 billion euros – representing around 95 million euros daily. However, managers are painfully discovering that when production stops in a "just-in-time" environment, this money won't wait for you. Irreplaceable production slots cause a domino effect across suppliers, transport schedules, and dealer inventory stocks. Revenue simply disappears.
This isn't just a problem for the United Kingdom, where JLR accounts for 4% of total goods exports. It's equally serious for Slovakia. The plant in Nitra, which produces Discovery and Defender models, ranks among the jewels of foreign investment in Central Europe. In a country where the automotive industry provides more than a tenth of GDP and supports 200,000 jobs, a cyberattack thousands of kilometers away immediately transforms into an urgent domestic crisis.
The attackers – whether they call themselves Hellcat, Scattered Lapsus$ Hunters, or something entirely different – have revealed a reality that the industry has been unwilling to acknowledge until now. The clean separation between digital systems and physical production lines is an illusion. When IT infrastructure gets hacked, robots stop functioning, conveyor belts halt, and the carefully choreographed ballet of modern industry collapses. All of this happening precisely in September, when dealers are feverishly clearing warehouses and trying to meet quarterly targets.
It's no wonder that manufacturing has become an irresistible target for cybercriminals. Downtime costs are astronomical, supply chains are stretched so tight that every outage immediately spreads further, and brand damage grows hour by hour. Management boards, which until recently viewed cybersecurity as a technical issue on the IT department's periphery, today recognize that it must be at the core of corporate strategy.
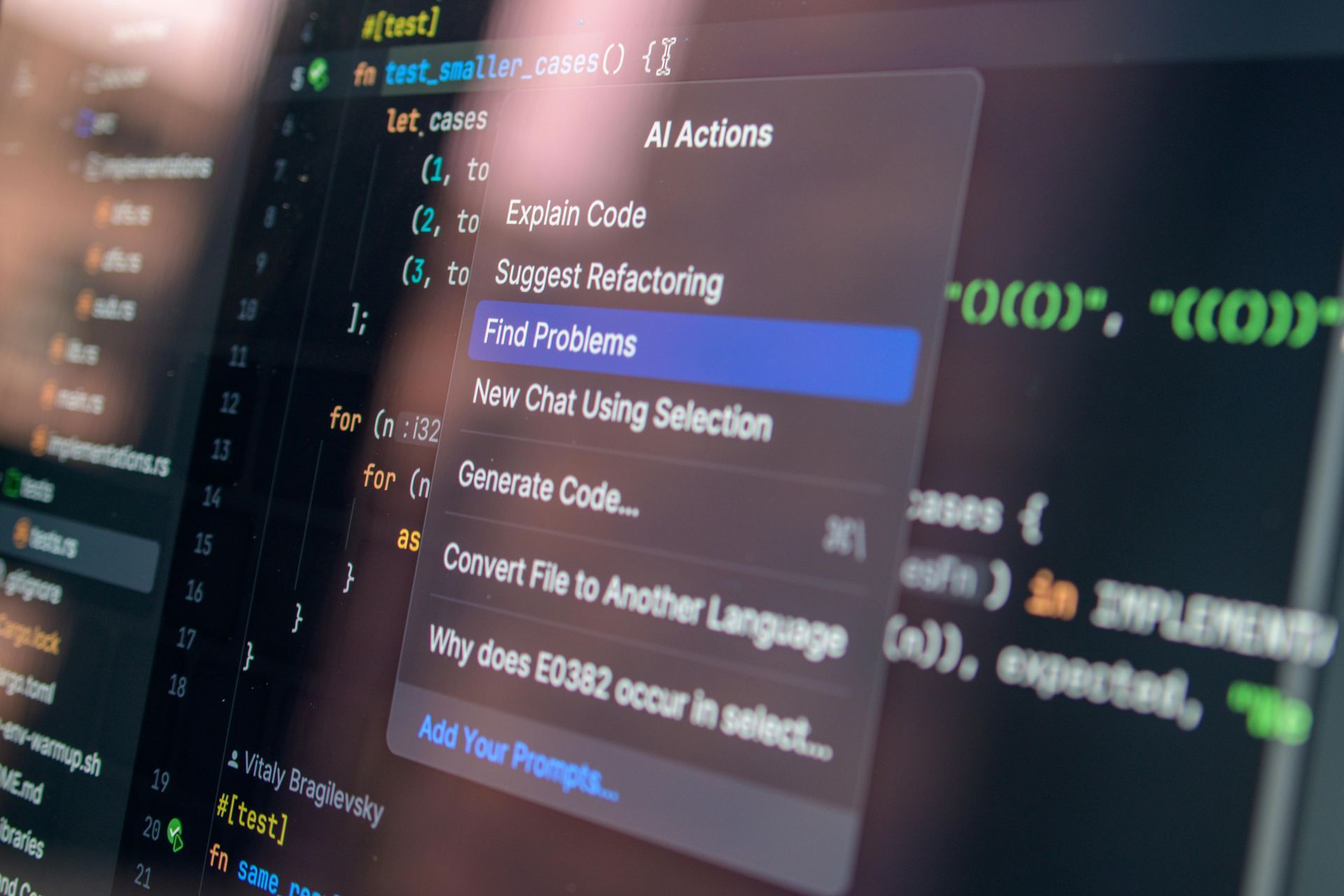
Old approaches – checking off ISO 27001 compliance boxes, annual penetration tests, firewall patches – seem almost nostalgically retroactive. Real resilience requires more radical solutions. Organizations must have continuous oversight of every corner of their IT and OT networks. They need to transition from a "castle and moat" model to zero-trust architecture, which assumes from the start that defenses will be breached. Within such timeframes, they must begin implementing post-quantum cryptography before quantum computers completely invalidate today's encryption methods. And perhaps most importantly – they must know how to restore operations from clean backups without accidentally restoring the malicious code that originally knocked them out.
The Jaguar Land Rover episode destroys the last illusions that cyber risks are separate from business risks. When a single attack can erase 100 million euros from daily revenue, it represents an existential threat to large industrial enterprises. For the United Kingdom of Great Britain and Northern Ireland and Slovakia, economies heavily dependent on automotive manufacturing, the lesson is clear. Today's most modern factories in the world, full of cutting-edge robotics and automation, can be brought down by an ordinary computer virus. This is the new face of industry in the digital era. It's not a question of whether another attack will come, but when companies and countries will be prepared when it happens.
Source: Michalko, Matej. “Keď hackeri pretnú otvorenú cestu: vo vnútri krízy za 95 miliónov eur denne v Jaguar Land Rover.” DefenceNews.sk, September 22, 2025. https://www.defencenews.sk/kyberbezpecnost/clanok/766426-ked-hackeri-pretnu-otvorenu-cestu-vo-vnutri-krizy-za-95-milionov-eur-denne-v-jaguar-land-rover/.